🧂 前言 今天會介紹另一個network forensic 工具-Zui ,另外也會介紹一下 Zui 當中使用到的 Zeek 與以及Suricata pcap 分析工具
Zui 下載連結:https://zui.brimdata.io/docs
Zui 它的前身是Brim , 是一款用於網路流量分析的工具,它提供了使用者友善的圖形化介面,可以讓使用者能夠快速分析與視覺化大量網路流量
這個工具裡面整合了兩個網路封包分析工具,分別是Zeek、Suricata
Zeek 連結:https://github.com/zeek/zeek
Zeek 是一個開源的網路安全監控工具,以強大的資料記錄功能聞名。它能將原始的 pcap 封包檔轉換成結構化的日誌,方便在 Zeek 內查詢與分析,快速提供網路行為的概覽。
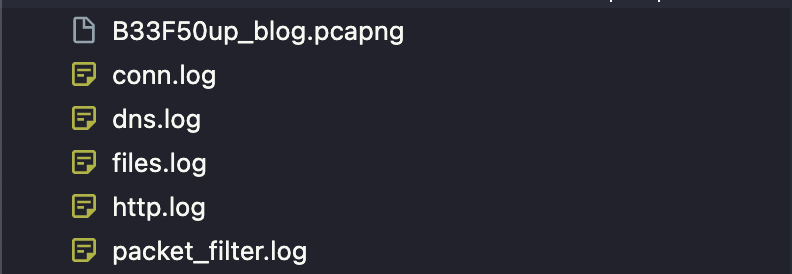
指令如下
1 zeek -C -r B33F50up_blog.pcapng
他會產生以下檔案
conn.log : 記錄了所有的網路連接
dns.log:記錄了所有的 DNS查詢活動
files.log:記錄了通過 HTTP 傳輸的檔案
http.log:這是一個 HTTP 協議的流量日誌,記錄了網頁瀏覽和API 請求
packet_filter.log:記錄了封包過濾器的配置
以下是http.log 的形式
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 1754678828 .272075 CAuRo91flufxXutAke 100.112.165.2 60665 192.168.1.125 5000 1 GET 192.168.1.125:5000 / - 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 - 0 24859 200 OK - - (empty) - - - - - - FA9Bk7Ikrr1LVrys - text/html1754678857 .820963 CIRhMK1X97Z1MzFRD1 100.112.165.2 60676 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 15 727 200 OK - - (empty) - - - FIUrzJ3sbt6deYBXf3 - text/plain FyILV9CHbcmUMGtc6 - text/json1754678865 .293310 CZnidTF5LIgaMzbRe 100.112.165.2 60677 192.168.1.125 5000 1 POST 192.168.1.125:5000 /system http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 141 185 200 OK - - (empty) - - - Fvs6lg41SIyuYsReh2 - - FqFYD91bNrEWRNR501 - text/json1754679070 .738945 CWlCIn4qK2ntw6CuJl 100.112.165.2 60757 192.168.1.125 5000 1 GET 192.168.1.125:5000 / - 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 - 0 24859 200 OK - - (empty) - - - - - - FG2QH72aF2jeG9CYC9 - text/html1754679165 .228123 C5V1Fn3nYAvFuSQeE 100.112.165.2 60778 192.168.1.125 5000 1 POST 192.168.1.125:5000 /system http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 141 287 200 OK - - (empty) - - - FnwtMr2TZ1qIS6LLmj - - Fq827u4xABcX563I21 - text/json1754679173 .669096 CWXpsv3zrBE7Lx66Sg 100.112.165.2 60779 192.168.1.125 5000 1 POST 192.168.1.125:5000 /system http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 144 13177 200 OK - - (empty) - - - FxvTqN3Pid7VWQP7y3 - - Fi4rGH32Y4P77kznf3 - text/json1754679180 .268390 Co6odn3WTbf9HKGcO6 100.112.165.2 60780 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 15 728 200 OK - - (empty) - - - FYW00SjDihqYC30xe - text/plain FQGbYm3SH1rsO8o9ng - text/json1754679196 .383809 CGjLWoznypKV0Pgt 100.112.165.2 60809 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 16 738 200 OK - - (empty) - - - FVCJDglco6ai9lzi4 - text/plain FB2a4L3x3ZELSSdCQ1 - text/json1754679223 .696243 C0s1KA7ZrfQvnIpj 100.112.165.2 60865 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 30 851 200 OK - - (empty) - - - FA2p79sD6MkhyaCEb - text/plain FwUGICEULGQRyBs78 - text/json1754679257 .891805 CtwrhY2Kw9bscBOsX7 100.112.165.2 60874 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 34 755 200 OK - - (empty) - - - FybSTDKXBk5dCiaYl - text/plain F55jsD1S1vWW8IVBY4 - text/json1754679265 .650887 CFgfqH2IasZxXsovkd 100.112.165.2 60875 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 30 869 200 OK - - (empty) - - - FtvRcZ3D5kRIP1ijy5 - text/plain FTYdr5iKtJX11Efma - text/json1754679315 .090163 CEAuN63ly0lHS2zRrj 100.112.165.2 60895 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 30 869 200 OK - - (empty) - - - Fyt7jP30AEKPs4C0Uj - text/plain F0zHt852ycC25Gpkf - text/json1754679319 .217264 CRWcyt2bda4K3g6Xub 100.112.165.2 60912 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 36 900 200 OK - - (empty) - - - FUAgus1sr4pPeGnidg - text/plain FqnOWw20dfXD0koyIi - text/json1754679354 .845803 CulPOq3A9IP8ab4Zqd 100.112.165.2 60981 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 48 769 200 OK - - (empty) - - - FZw17aZHAnZltVkJ - text/plain FQvAYSOVPIbUCfRm7 - text/json1754679406 .575000 C9iy0scrJKJuDpi07 100.112.165.2 61207 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 49 2621 200 OK - - (empty) - - - FiejrYnJjwTaJ5db7 - text/plain FKZoSb4yddnL4uzkZf - text/json1754679827 .575533 CV2dqm3aNuGOi4EC0h 100.112.165.2 63113 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 36 912 200 OK - - (empty) - - - FDaXYp2bh8hJpHMYCi - text/plain FdsBU41nDrcCQ9mTV9 - text/json1754679851 .757452 CWSzgl4AsTyJVyRpJf 100.112.165.2 63213 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 44 800 200 OK - - (empty) - - - FAGwfWDdjCLhcrZX2 - text/plain F89dhl1uFy7r4oRtf - text/json1754679859 .655497 C0LErP2jTxCqKmUESd 100.112.165.2 63216 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 47 781 200 OK - - (empty) - - - FoNYJj2QlLyZkd9tEe - text/plain FUaGCH2RbcOlDQcaOi - text/json1754679875 .655339 CqC0qj2SMoQnSfaju6 100.112.165.2 63217 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 31 762 200 OK - - (empty) - - - FRGjia4iHeyPzIDRC3 - text/plain FwGgDTGi2gHDik2P5 - text/json1754679999 .499748 CtN1Vk4RrwIRGOgwHc 100.112.165.2 63280 192.168.1.125 5000 1 POST 192.168.1.125:5000 /ping http://192.168.1.125:5000 / 1 .1 Mozilla/5 .0 (Macintosh; Intel Mac OS X 10 _15_7) AppleWebKit/537 .36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537 .36 http://192.168.1.125:5000 142 836 200 OK - - (empty) - - - FFJx4j4PnbpIi0mfD6 - text/plain FYpDmc37JMpCuz4Zac - text/json
另外他也會根據 pcap 檔產生其他log ,參考網址:https://docs.zeek.org/en/master/logs/index.html
Suricata 連結:https://suricata.io/
Suricata 是一個開源的入侵偵測系統(IDS)與入侵防禦系統(IPS),以深度封包檢測、流量分析與威脅偵測聞名。能使用 Suricata 的龐大規則集快速評估網路資料並辨識異常。
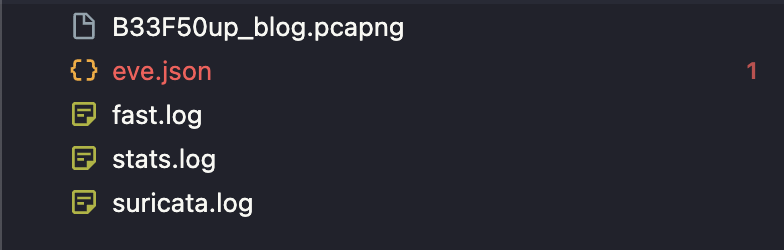
指令如下
1 suricata -r B33F50up_blog.pcapng
他會產生四個檔案
eve.json : Suricata的結構化日誌檔案,包含多種事件類型的詳細記錄
fast.log : Suricata 快速警報日誌,包含檢測到的安全威脅警報
stats.log : Suricata 運行統計資料,包含詳細的系統運行統計
suricata.log : Suricata 主要運行日誌,包含系統啟動和運行資訊
以下是 fast.log 資訊
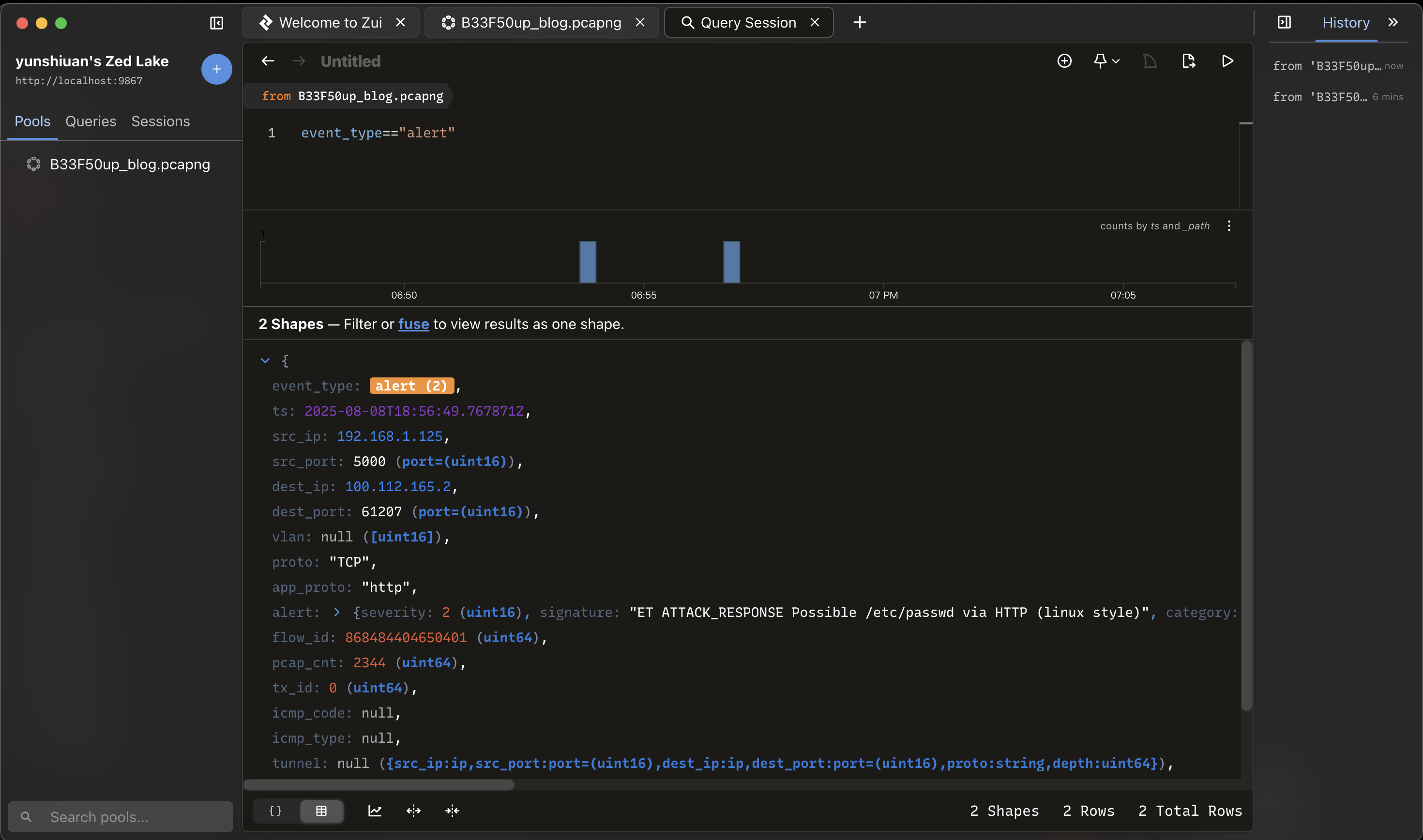
1 2 08/09/2025 -02 :53:47.165861 [**] [1:2019284 :3 ] ET ATTACK_RESPONSE Output of id command from HTTP server [**] [Classification: Potentially Bad Traffic] [Priority: 2 ] {TCP} 192.168.1.125 :5000 -> 100.112.165.2 :60865 08/09/2025 -02 :56 :49.767871 [**] [1:2002034 :13 ] ET ATTACK_RESPONSE Possible /etc/passwd via HTTP (linux style) [**] [Classification: Information Leak] [Priority: 2 ] {TCP} 192.168.1.125 :5000 -> 100.112.165.2 :61207
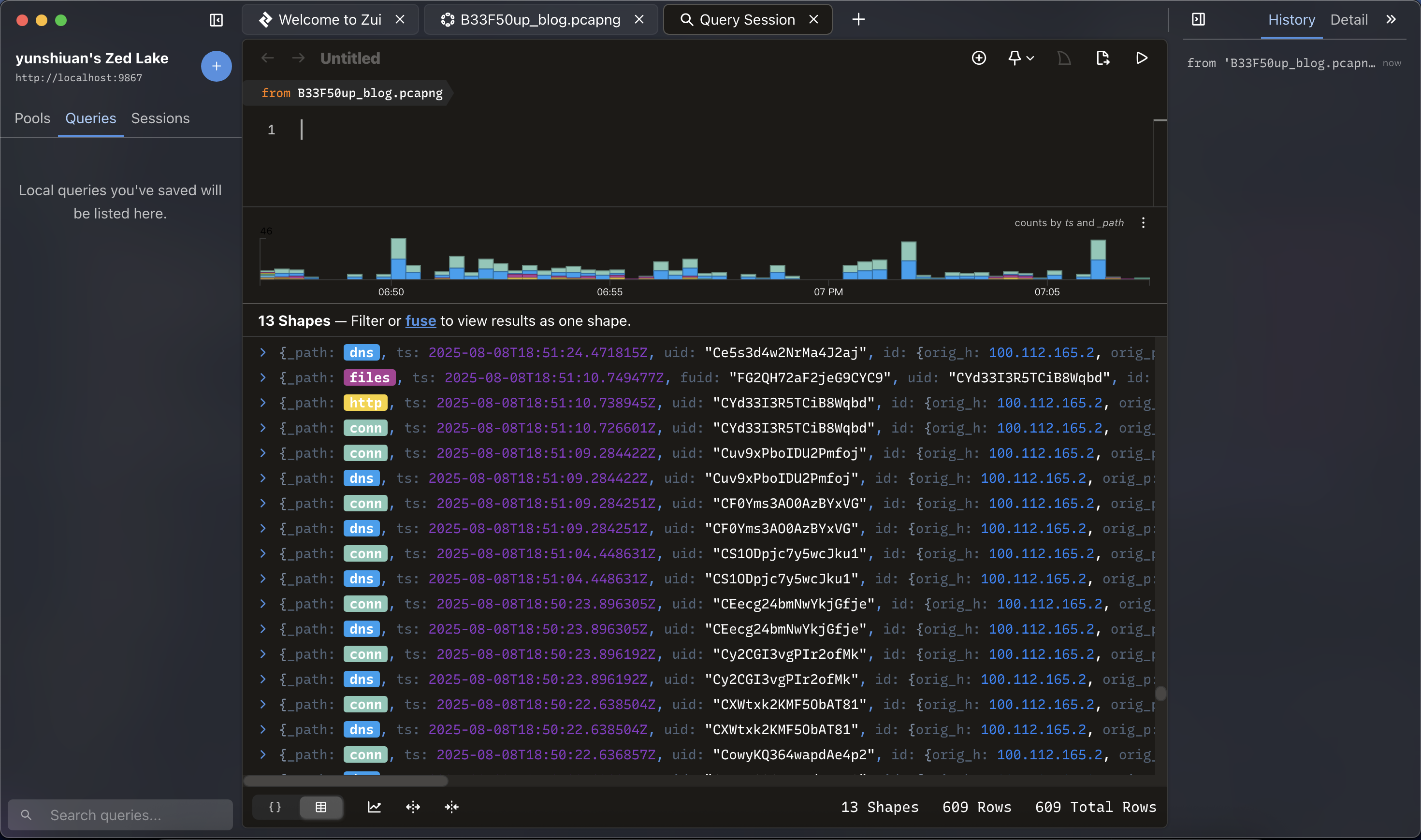
總結來說 Zui 的做法是先用 brimcap 將 pcap 送到 Zeek/Suricata 做 summary/log,再在 Zui 內用 correlation view、alert 視窗、或 detail pane 分析事件與原始封包。
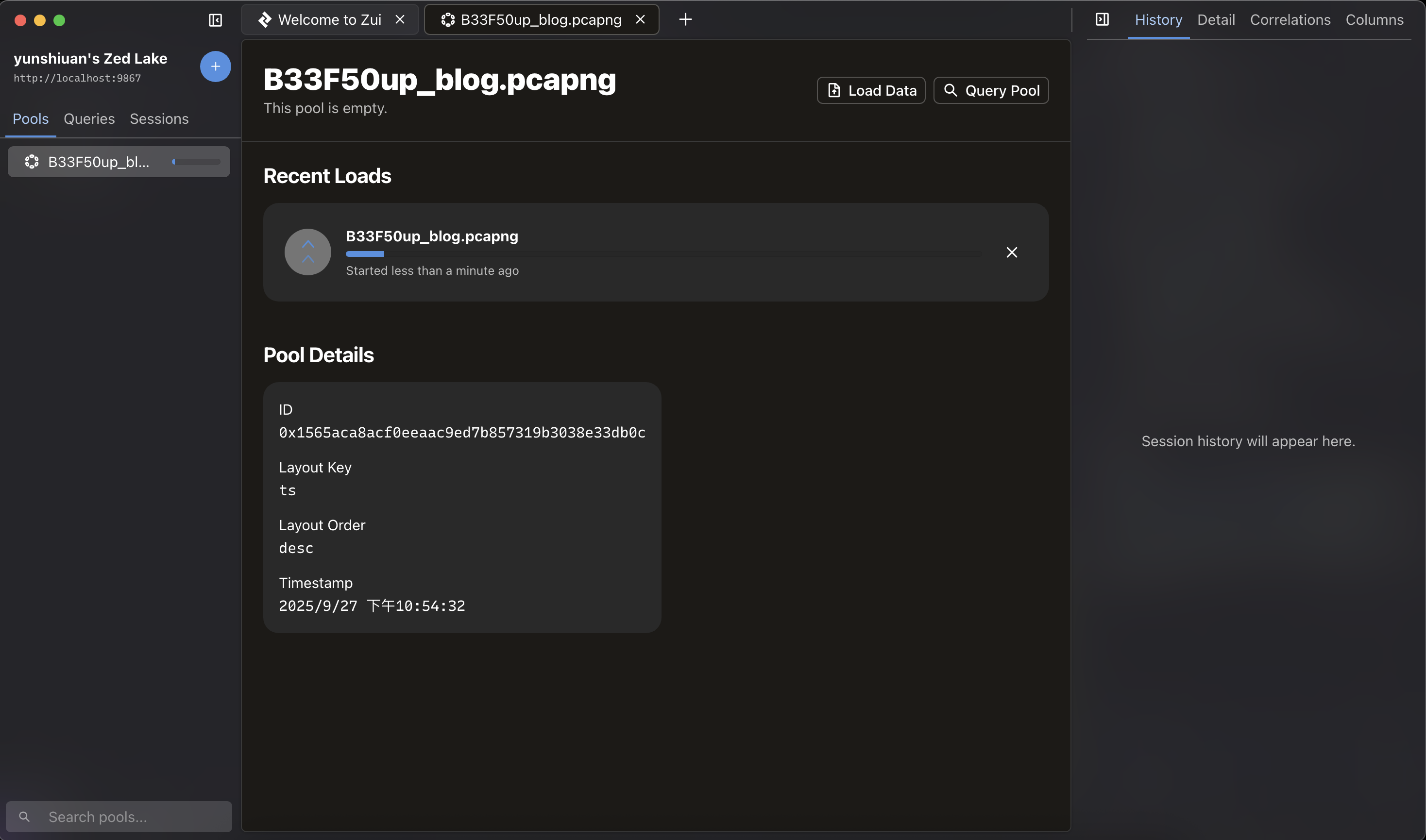
所以只要將pcap 封包丟進去 zeek ,他就會開始進行分析
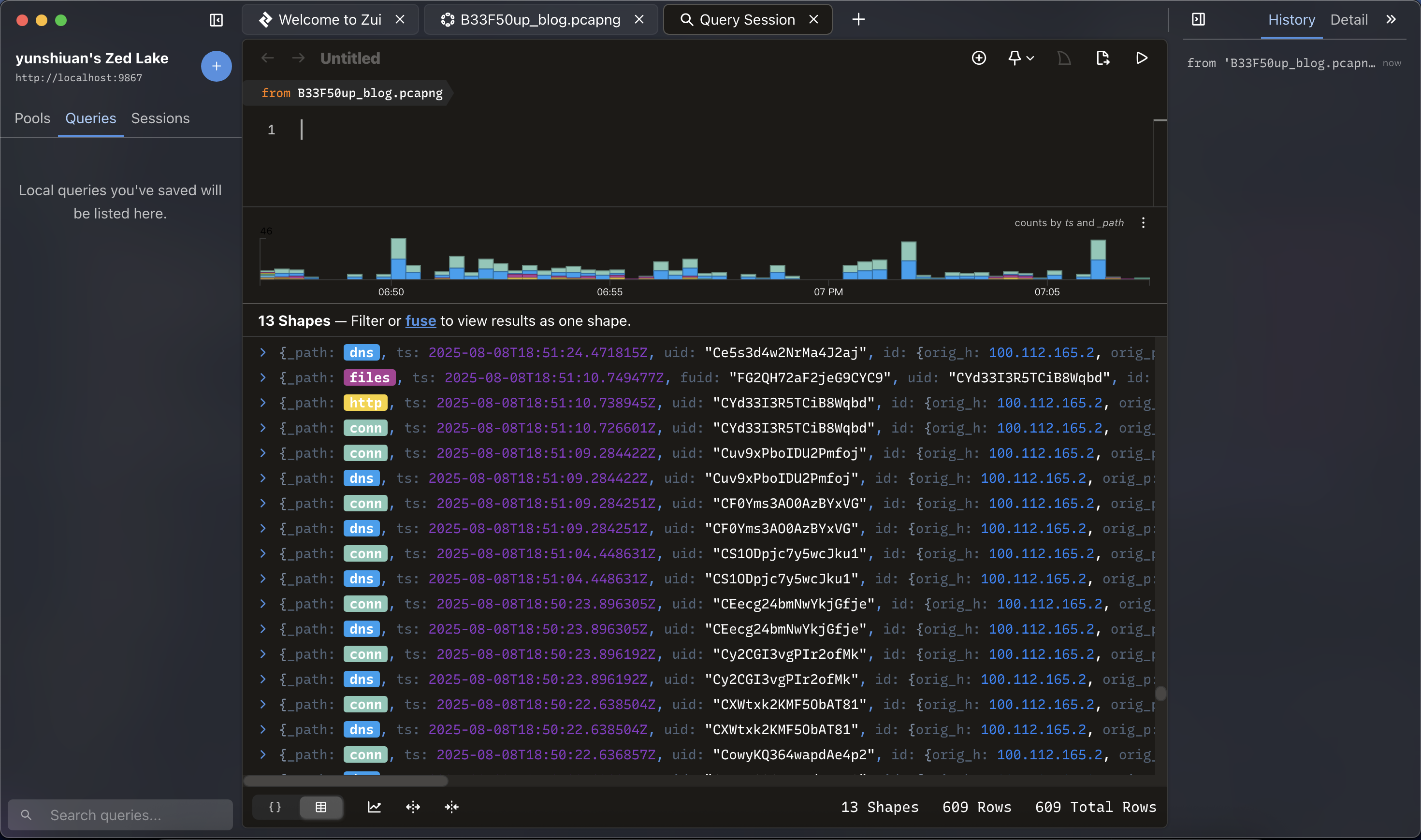
分析完後按下Query Pool 就可以看到視覺化的頁面
另外 Zui 使用 Zed(或稱 Zed query / SuperSQL)來做過濾與轉換查詢可以更快處理大量資料
以下分享幾個操作
首先可以篩選出Suricata 警報
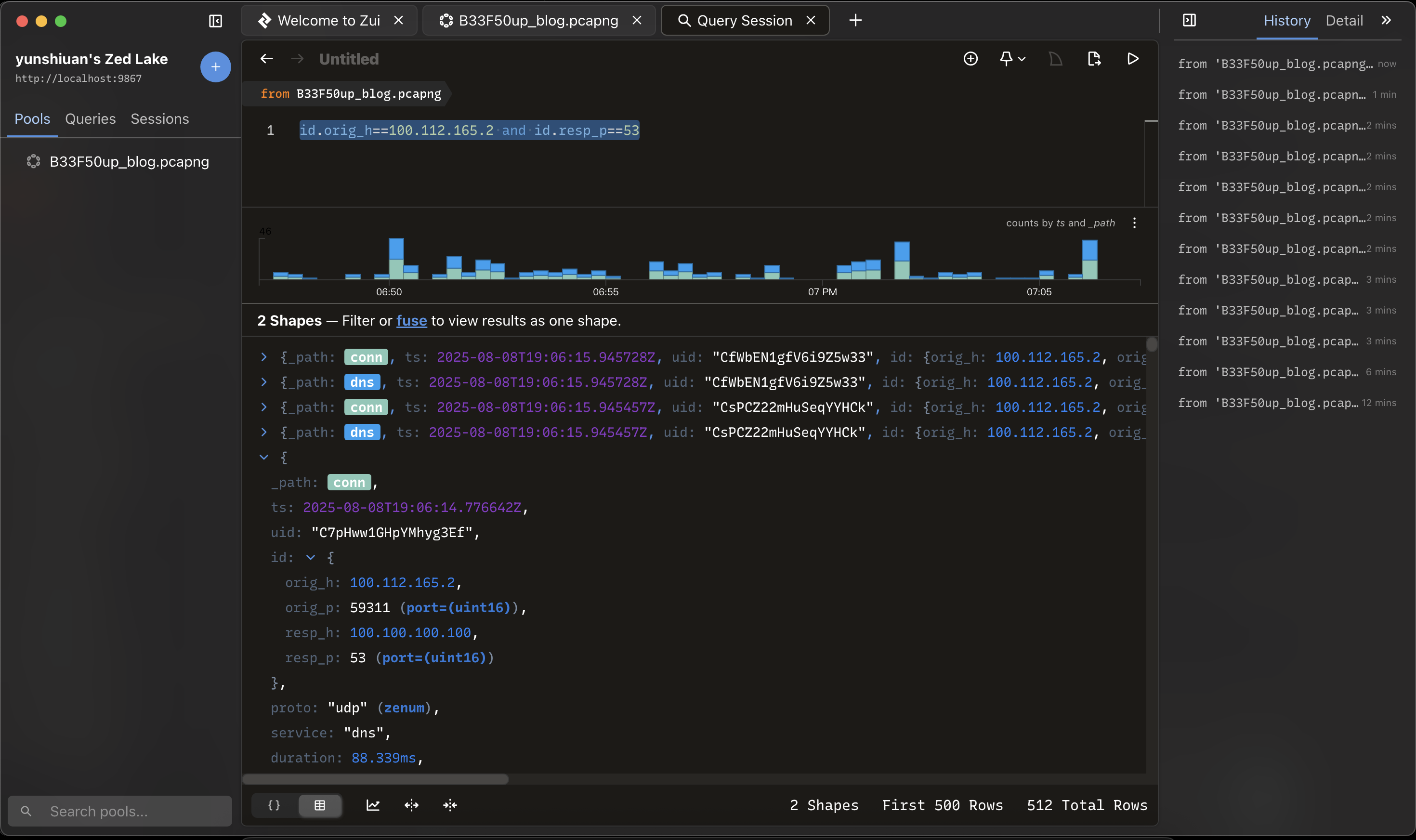
也有像wireshark 一樣可以篩選 ip scr or ip dst
1 id .orig_h==100.112.165.2 and id.resp_p==53 #來源ip = 100.112.165.2 目標port = 53
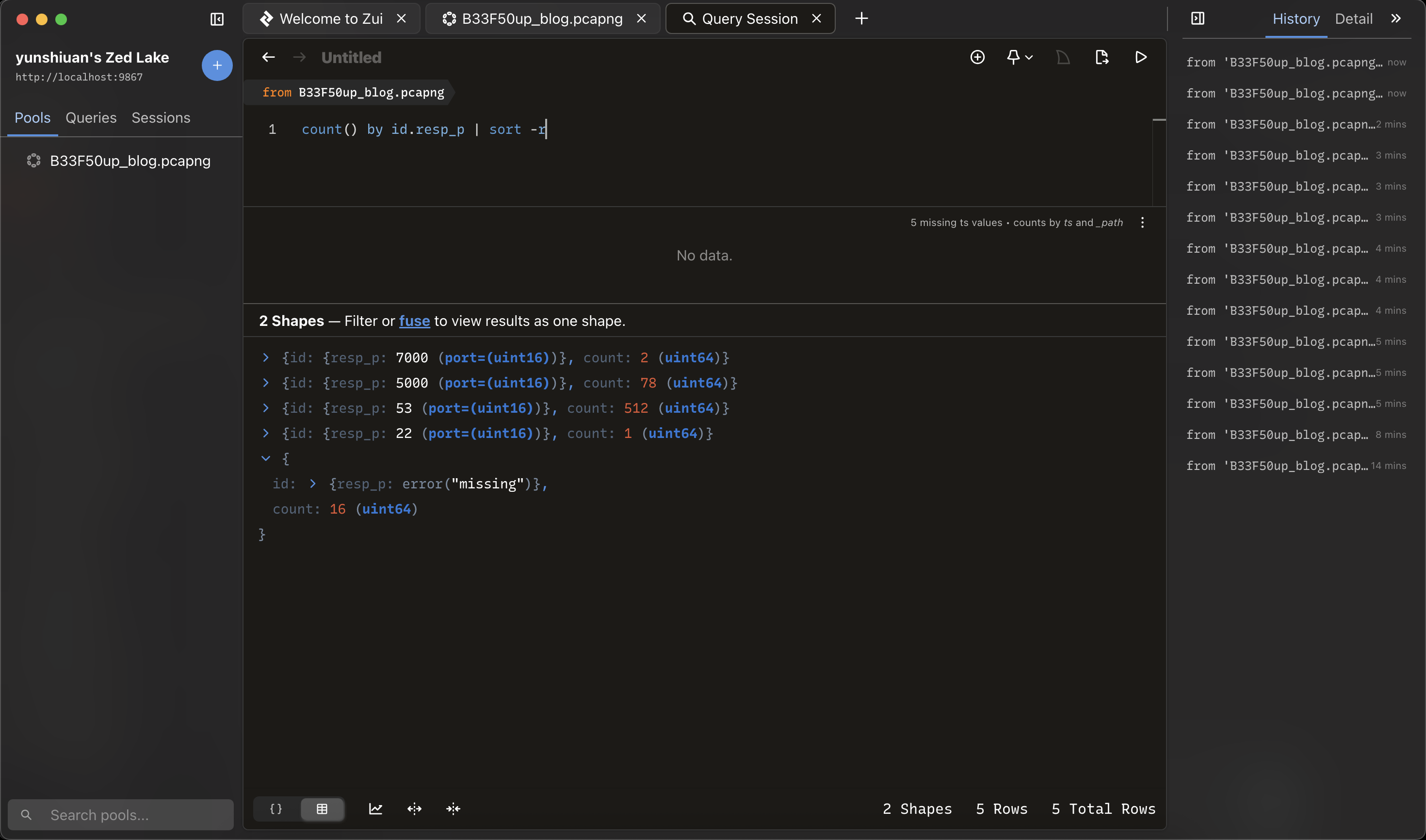
另外他也可以進行統計與排序
1 count () by id .resp_p | sort -r
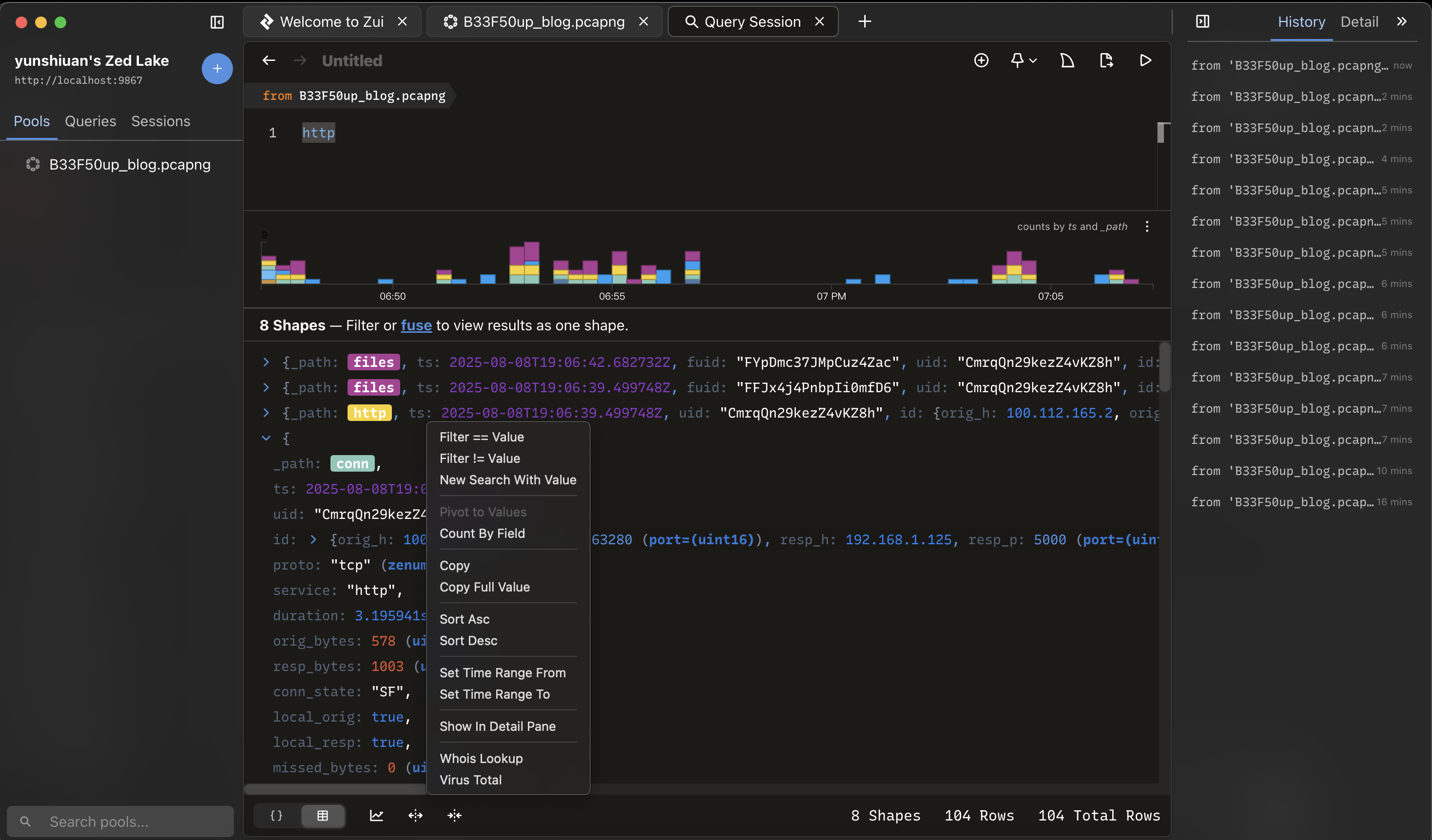
對你想要篩選的資料按右鍵可以自動生成查詢指令
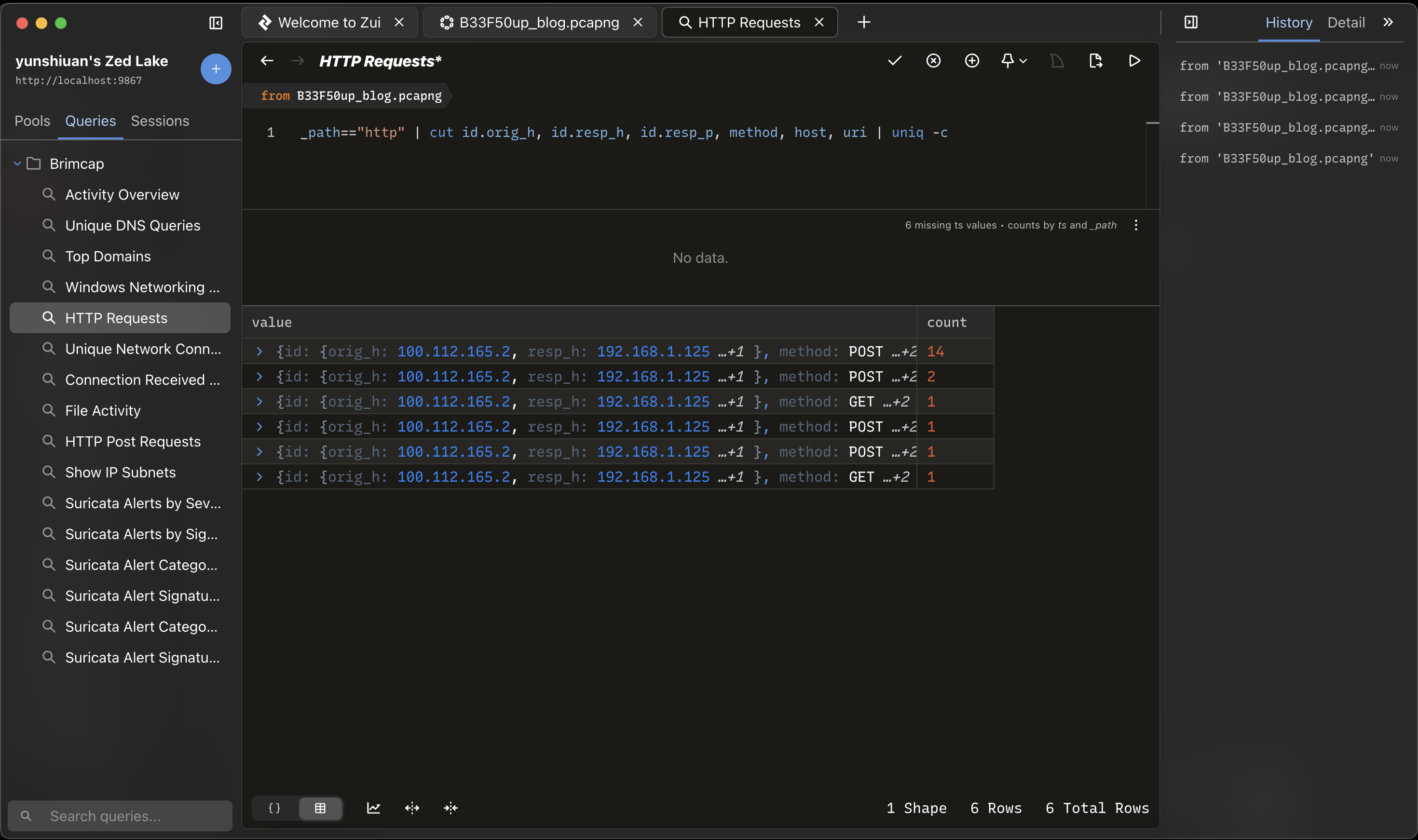
最後也可以下載官方提供預先寫好的查詢
連結:[https://github.com/brimdata/brimcap?tab=readme-ov-file#brimcap-queries
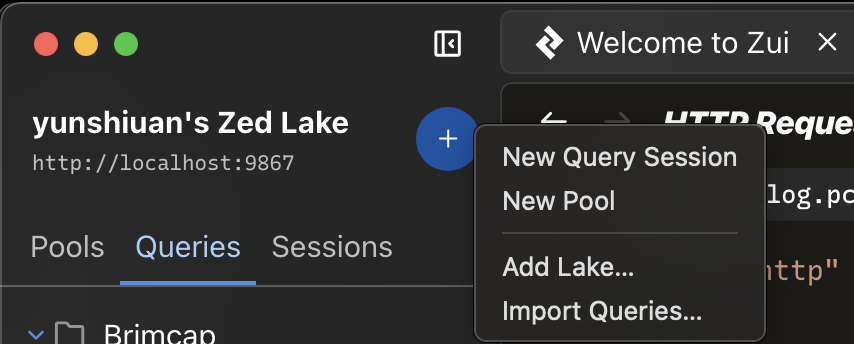
](https://github.com/brimdata/brimcap?tab=readme-ov-file#brimcap-queries)下載後queries.json 後按下+的藍色按鈕,點選Import Queries
把剛剛下載的json 檔丟進去,就會匯入預先寫好的query
總結 今天介紹了Zui 以及其中Zeek 與Suricata功能,也有分享zui 的基本操作,zui 在解一些CTF 題時也會有奇效,雖然沒辦法查看詳細封包內容,但在快速查詢可疑行為或可疑流量時會很好用。